Why Modern Linux Security Needs a Prevention-First Approach
March 31, 2026
Linux sits at the heart of today’s digital infrastructure, powering cloud platforms, virtual machines, application servers, databases, and mission-critical workloads that businesses rely on every day. It’s stable, flexible, and battle-tested. But its popularity has also made it a growing target for attackers who now view Linux environments as high-value entry points.
If your organization depends on Linux, securing these systems is no longer optional; it’s essential.
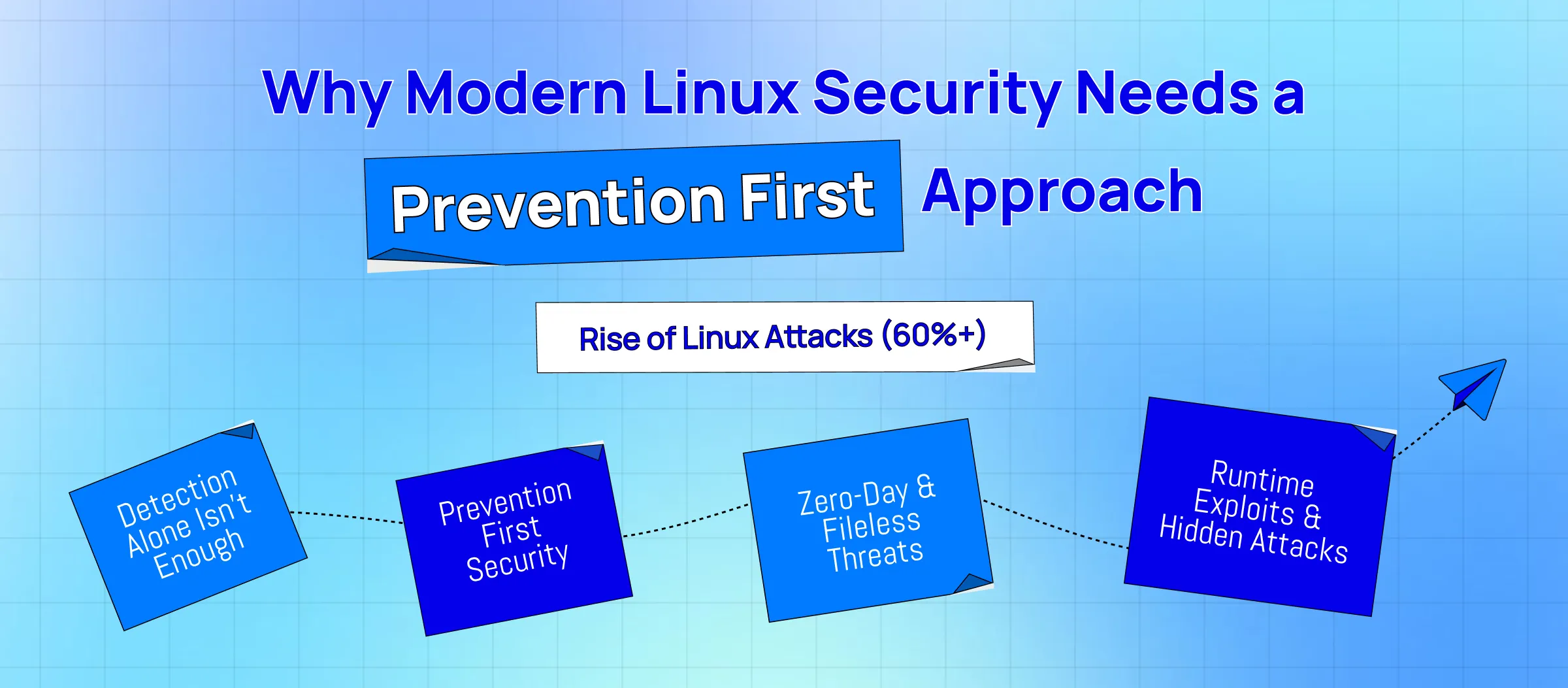
The Threat Landscape for Linux Is Changing Fast
Over the past few years, attacks on Linux have skyrocketed. Between 2022 and 2023 alone, Linux-based attacks accounted for more than 60% of malware infections globally. And it’s not hard to see why:
- Linux hosts core business applications
- It powers cloud and hybrid environments
- It stores sensitive enterprise data
- Many workloads run 24/7 with privileged access
Attackers know that compromising a Linux server can have far-reaching consequences, from data theft and operational disruption to multi-system compromise across your network.
What’s more alarming? Most organizations still rely heavily on traditional defenses like NGAV, EPP, and EDR/XDR. While these tools are great at catching known threats, they struggle against:
- zero-day exploits
- memory-only (fileless) attacks
- living-off-the-land techniques
- runtime manipulation
- evolving ransomware strains
These sophisticated attacks slip past detection tools and exploit a 30% security gap that leaves Linux systems exposed.
Why Detection-Based Security Isn’t Enough for Linux
Traditional security tools operate on a basic principle:
detect something suspicious → alert → respond.
But modern Linux attacks don’t always give you something obvious to detect. They often:
- never touch the file system
- hide in runtime memory
- piggyback on legitimate processes
- exploit unpatched or legacy applications
- blend into normal system activity
When tools rely on signatures, patterns, or behavioral history, new and unknown threats simply fall through the cracks.
Linux’s diverse ecosystem makes things even harder, with dozens of distributions, custom configurations, outdated dependencies, and mission-critical workloads that can’t be patched instantly. Put simply, Linux’s flexibility is its power and also its vulnerability.
Morphisec Brings a Prevention-First Strategy to Linux Security
This is exactly where Morphisec changes the game.
Instead of detecting threats after they appear, Morphisec’s Automated Moving Target Defense (AMTD) prevents attacks before they can execute, making your Linux environment unpredictable and hostile to attackers.
Here’s how Morphisec keeps Linux workloads secure:
1. Dynamic System Hardening
Morphisec constantly shifts and randomizes key application memory and runtime structures.
Attackers expect things to be in predictable places, but AMTD moves them, creating a moving target.
If malicious code tries to exploit a memory location? It hits a decoy instead and collapses immediately.
2. Advanced Attack Surface Reduction
By proactively blocking the most common exploit primitives that attackers rely on, Morphisec significantly reduces your exposure, even on older or unpatched systems.
3. Ransomware & Data Exfiltration Prevention
Ransomware and data theft attempts are stopped deterministically inside runtime memory, before encryption or exfiltration begins.
4. Broad Linux Distribution Support
Morphisec supports leading distros across physical, virtual, and cloud environments, including:
- Red Hat
- Ubuntu
- Debian
- SUSE
- Oracle Linux
- Rocky Linux
- AlmaLinux
- Amazon Linux
Your entire environment stays protected, no exceptions.
Why Linux Security Teams Choose Morphisec
Organizations adopting Morphisec benefit from:
Closing the runtime memory protection gap: Covering the 30% of attack techniques that legacy tools simply don’t see.
Protecting core workloads: Including application servers, Kubernetes nodes, and virtualized environments.
Reducing noise and alert fatigue: Morphisec generates near-zero false positives, no constant tuning, and has no detection chases.
Lightweight, production-safe performance: A tiny footprint that’s optimized for high-performance environments.
Strengthened compliance posture: Protection against ransomware, lateral movement, and risk factors tied to modern Linux breaches.
Final Thoughts: The Future of Linux Security Is Prevention
Linux has become the backbone of enterprise IT, and attackers know it. As threats evolve, organizations can’t rely solely on detection-based tools that were designed for a simpler era.
A prevention-first strategy is now the only way to ensure that your Linux workloads, applications, and critical systems remain resilient.
Morphisec’s AMTD technology brings a fundamentally smarter, proactive approach to Linux security—one that blocks attacks before they execute, reduces your attack surface, and strengthens your defenses without slowing you down.
If you’re serious about protecting your Linux infrastructure against today’s most advanced threats, it’s time to see what true prevention looks like.
Request a demo and discover how Morphisec secures Linux environments with unmatched precision and performance.
Keep reading about
LEAVE A COMMENT
We really appreciate your interest in our ideas. Feel free to share anything that comes to your mind.
Our 16 years of achievements includes:
-
10M+
lines of codes
-
2400+
projects completed
-
900+
satisfied clients
-
16+
countries served