7 Emerging Cybersecurity threats you can’t miss out in 2021
Published: May 20, 2021
Last Updated: June 7, 2024
Introduction
Mobile security tops the list of concerns for many companies today. The trend is such that all employees regularly access corporate data mostly from their smartphones. And that makes keeping sensitive information out of the wrong hands a daunting task. Today we will share with you the cybersecurity threats that businesses need to pay more attention to, in the coming year 2021.
1. Data leakage
Data leaks are already seen as one of the most worrying threats to enterprise security in 2020. And when it comes to data breaches, the ability to find or recover is almost absent. It is predicted that 28% of businesses will experience a data breach at least once in the next two years.
According to professional insurance providers, “accidental disclosure” was and is the leading cause of data breaches reported by healthcare organizations in 2019 – 2020. The problem, combined with personal information leaks, accounts for nearly half of all reported breaches.
2. Scams from social networks
91% of cybercrime starts with an email. Accordingly, most attacks are malware-free, with hackers relying solely on tactics like impersonation to trick people into clicking dangerous links or providing sensitive information themselves. Specifically, phishing was up 65% in 2019, and mobile users are most at risk. The company said that there are currently a lot of mobile email applications that only display the sender’s name, making it easy to fake a message and trick users into thinking that an email comes from someone they know and trust.
Not only email, but the report also shows that up to 83% of phishing attacks in 2019 were carried out via messages from apps like Facebook Messenger, WhatsApp, games, and social media services.
3. Wi-Fi wave interference

Companies’ mobile devices using Wi-Fi waves are now three times higher than mobile phone waves, of which nearly a quarter of devices connected to open Wi-Fi networks are not secure and 4% of devices have experienced at least one intermediate attack (someone intercepted or overheard communications between the two parties) in the most recent month.
Cybersecurity experts also warn that network spoofing has increased significantly in 2019-2020, while less than half of users are concerned with securing their connection while traveling / business trip or connecting to a public network.
4. Attack on cryptocurrencies
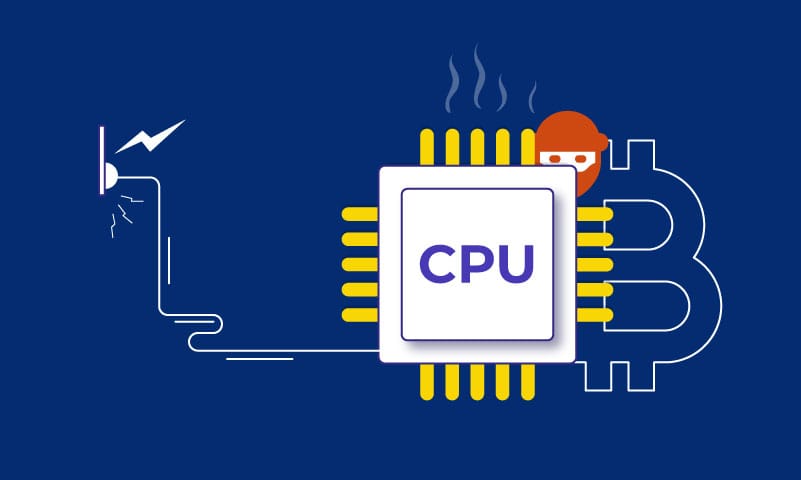
Cryptocurrency mining is a new way criminals use to make money with your device hardware. When opening a website in its browser, cryptojacking malware can maximize CPU usage to mine cryptocurrency, and it is becoming more and more popular. This is a very new form of attack that the victim is often unaware of. In the process of mining, attackers use your company’s devices for a profit.
Mining cryptocurrencies involves running complex mathematical equations, using a lot of CPU power. In such an attack, the mining software maximizes the computer’s CPU. As a result, your computer will run slower, use more energy and generate more heat. If you use a laptop the battery drains quickly, while on a desktop it sucks up more electricity and increases the company’s electricity bill.
5. The drawbacks in supply chain

Supply chains are an important part of the global business of every organization and enterprise and are the backbone of today’s global economy. In the supply chain, a range of valuable and sensitive information is often shared with suppliers, and when information is shared limits the ability to directly control. This increases the risk of data security, integrity, or availability.
In 2019, organizations and businesses need to focus on the weakest points in their supply chain. Not every security compromise is preventable in advance, but being proactive means you and your supplier will be able to react faster and smarter when something happens.
To deal with information risks in the supply chain, organizations and businesses should apply strong, scalable, and repeatable processes that are commensurate with the risks faced. Supply chain information risk management should be integrated into existing supplier management and procurement processes. This willingness can dictate the company’s competitiveness, financial health, stock price, or even the survival of a business when a breach occurs.
6. Super-fast connections bury self-defense

An affordable, ultra-fast gigabit connection offers enormous potential to open up new markets and opportunities for businesses, especially in areas such as teleconference, entertainment, and embedded devices. But those super-fast transmissions also open up new opportunities for crime. At the moment, the challenge for organizations is how to deal with all of the problems posed by ultra-strong connections – the higher risk of “exposure” to certain types of attacks and sabotage.
To prepare for these threats, we recommend that you implement powerful recovery plans with your suppliers, as well as identify and evaluate the risks of embedded devices.
7. Physical device violation

Last but not least, a very real threat. A lost or unattended device is a major security risk, especially if it doesn’t have a strong PIN or password and fully encrypts the data.
According to a Ponemon Institute (USA) study, 35% of experts said that their working devices do not have measures to enforce the security of company data. Worse yet, nearly half of people surveyed said they don’t have a password, PIN, or biometric security that protects their device, and about two-thirds say they don’t use encryption. Similarly, 68% of respondents said that they share their personal and work account passwords for access via their mobile devices.
Conclusion
Whether an organization or an individual, the threat of cybersecurity attacks remains an existential threat. It is never too late to prepare your own organization for a defense plan and a scenario to respond to possible attack scenarios for your data infrastructure. Along with that, always keep a close eye on where your database traffic and sources come from, and work with your network protection provider to minimize the damage caused by a potential attack. Taking the initiative in all situations is how your organization should prepare now.
Keep reading about
LEAVE A COMMENT
We really appreciate your interest in our ideas. Feel free to share anything that comes to your mind.
Let's Craft Brilliance
Just exploring? Let's think out loud together. We would love to hear from you. Come, let's get started!